Back-End Development
Robust databases, row-level security, real-time capabilities, edge functions, and authentication, all configured and production-hardened. We handle the back-end so your team ships features, not infrastructure.
A production back-end is more than a database and some API routes. It's row-level security, audit logging, edge functions, real-time subscriptions, proper auth flows, and a deployment strategy that doesn't page you at 3am. We handle all of it. Our back-ends are configured for production from the first deploy, which means you don't spend your Series A budget re-architecting what we built at seed.
What's Included
How We Work
Schema Design
Full data model, relationships, and constraints defined before any application code is written.
API & Security
Row-level security, auth flows, edge functions, and real-time subscriptions built to production standard.
Deploy & Monitor
CI/CD, environment management, error tracking, and performance baselines before the first real user.
Tech Stack
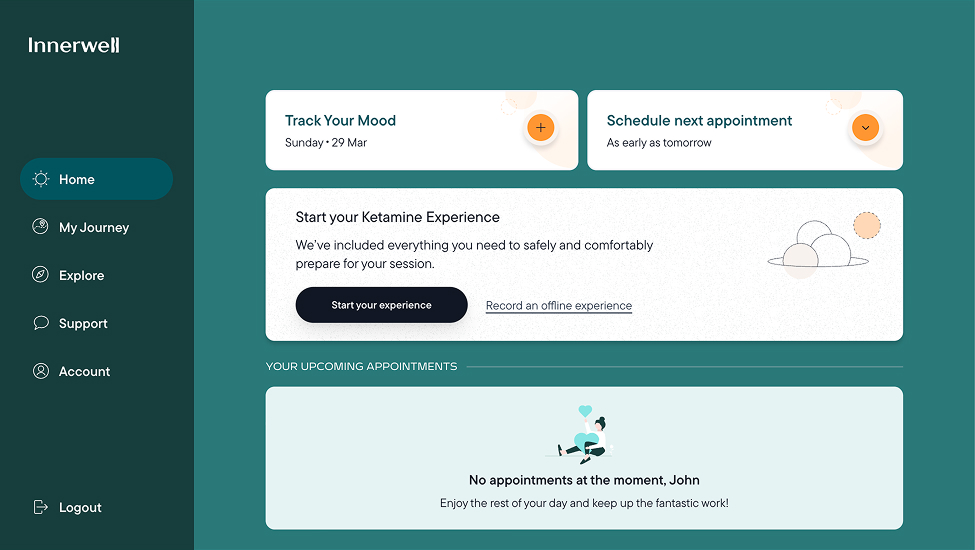
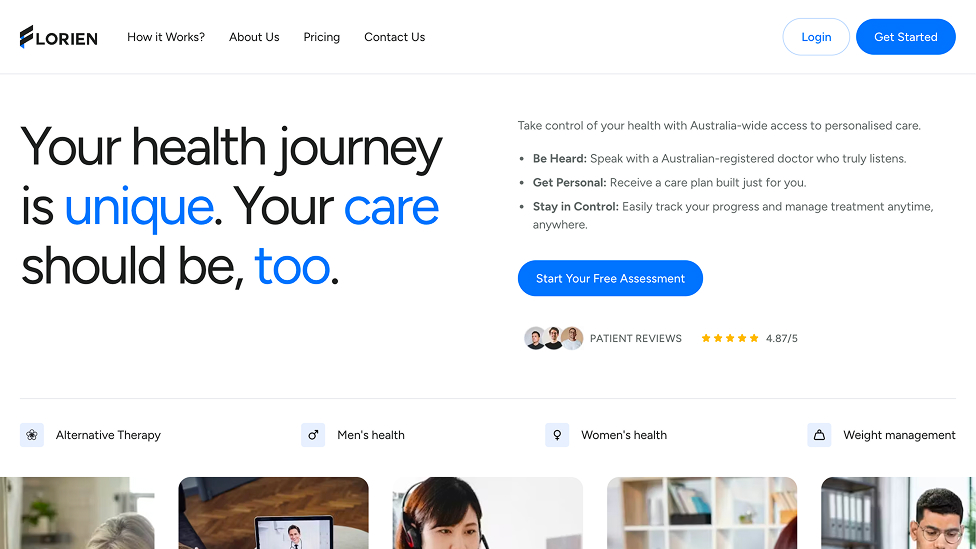
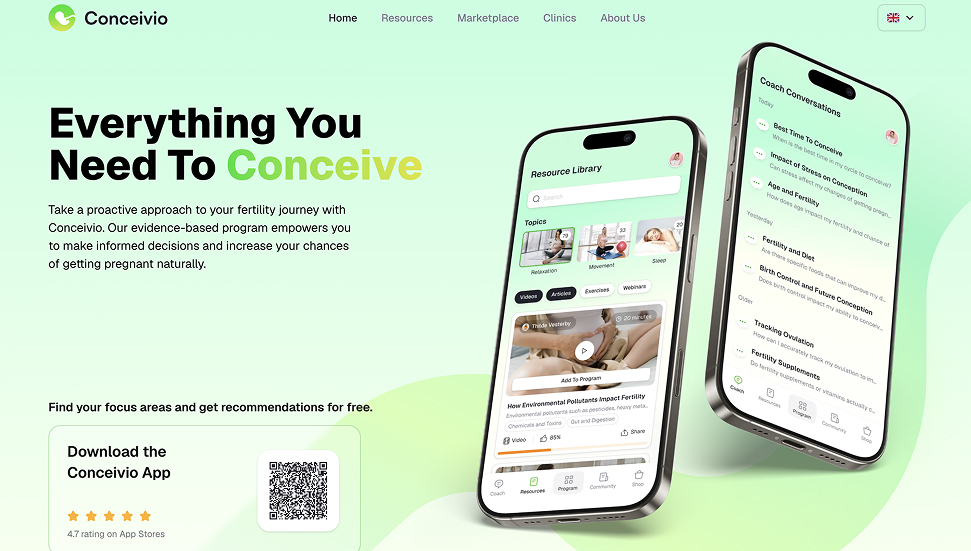
Work We've Done
From the Blog
Choosing the Right Tech Stack for Your Startup in 2026
Speed of development, production scalability, and zero DevOps overhead. We break down how to choose a front-end and back-end stack that lets small teams ship fast without painting themselves into a corner.
Building HIPAA-Compliant Apps: A Practical Guide
Row-level security, PHI-safe storage, audit logging, and BAA agreements. Everything you need to know to build healthcare applications that pass compliance reviews.
Common Questions
Why Supabase over a custom backend?
Supabase gives you Postgres with no vendor lock-in, row-level security, auth, realtime, storage, and edge functions without stitching five services together. For most startups, it removes months of infrastructure work.
How do you handle authentication?
Supabase Auth for most projects. That gives you OAuth, magic links, and session management out of the box. RLS policies integrate auth with your data access rules at the database layer, not just the API layer.
Can you work with an existing codebase?
Yes. We audit the schema and security posture first, then extend without breaking what works. We've inherited databases of every shape and fixed the problems that were waiting to cause incidents.
Ready to get started?
Tell us what you're building. We'll have an architecture plan and timeline back to you within 24 hours.